Cyber security company Symantec has identified a Chinese hacking group (also called an Advanced Persistent Threat – APT) known as Thirp, which the company believes has the ability, potentially, to take over the computers of satellite communications operators in Southeast Asia and the United States that control their satellites.
Reuters reports that security researchers at Symantec described that a “sophisticated hacking campaign”was launched via computers in China into satellite operators, defense contractors and communications companies in the United States and Southeast Asia. Reuters also reported that Symantec said the effort appeared to be motivated by national espionage goals. Symantec said it has already provided technical information to the US Federal Bureau of Investigation and Department of Homeland Security, as well as to other security agencies and public defence agencies in Southeast Asia.
Symantec released details of its findings exclusively to Reuters ahead of its public release.
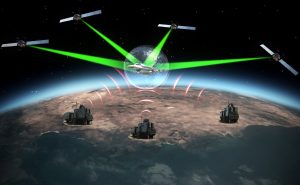
Interception capabilities by hackers are rare, and the researchers could not say what communications were taken, if any. The hackers attacked computers controlling satellites, which could have allowed them to change satellite positions and disrupt data traffic, Symantec said.
“Disruption to satellites could leave civilian as well as military installations subject to huge (real world) disruptions,” said Vikram Thakur, technical director at Symantec. “We are extremely dependent on their functionality.” Such disruption could have impacted telephone and Internet communications, as well as data used for mapping and positioning.
Symantec also reported that the hackers have been removed from the systems.
Thirp, which may also be known by other names, was active from 2013, but disappeared for about a year before reappearing when the last campaign started, about a year ago. Thakur explained to Reuters that Thirp developed new tools and began using more widely available administrative and criminal programs during that time.
Other security analysts have also recently tied sophisticated attacks to recently-dormant Chinese groups, and there could be overlap. Thirp infected servers, rather than users’ computers, in this attack, though it was unclear how Thirp gained entry to them.. In past attacks, it depended on trick emails with infected attachments or led recipients to malicious links.
Symantec, based in Mountain View, California, provides the most widely used paid security software for consumers and higher-end software and services for companies and public agencies.





